[Note: links may contain marketing material]
Yossi called me, introducing himself as an investigator of cybercrime. He asked me if I'd been the victim of cybercrime in the past year. I said I had, and he told me he'd been hired by an Israeli company that fell victim to fraud and transferred payment to an unknown address instead of to its supplier.
Yossi told me that during his investigation he came across over twenty such cases, including mine. He added that he thinks they were all done by the same conman, who we'll call here "crooked Jeff".
Phishing and cyber fraud are a daily occurrence, and it's a good idea to learn from others' bad experiences.
The Fraud I Fell for and a Happy Ending
I represent in Israel a Danish company called Hexa-Cover, which manufactures floating reservoir covers. In September 2020 we were just about to close a big deal with an Israeli client.
Crooked Jeff found out about the deal, monitored communications between me and Soren, Hexa-Cover’s CEO, and learned to copy Soren’s writing style.
Hexa-Cover’s domain name is https://www.hexa-cover.dk/, and about three weeks before our deal was finalized, crooked Jeff purchased the domain name https://www.hexa-cover-dk.com, and registered email addresses similar to those used by Hexa-Cover personal. For example, XXX@hexa-cover.dk was changed to XXX@hexa-cover-dk.com.
Looking at those addresses now you can see how different they are, but during the normal course of your work, the difference is easy to miss.
First, how often do you scrutinize the email addresses you frequently work with? Especially when, in some email platforms, you see only the name of the sender, not the address. You have to click on the name to see the full address.
Second, Soren always includes at the end of his emails photos of covered reservoirs. Crooked Jeff copied those photos, and Soren’s signature, so the emails he sent were visually similar to the original ones.
Third, style and content. As mentioned above, crooked Jeff studied the communication between me and Soren, so his style of writing was the same as Soren’s.
Crooked Jeff inserted himself between us in our communications. Some emails passed between me and Soren, but most he wrote himself - all while giving relevant answers and appearing to be the real Soren.
It wouldn’t surprise me if emails from me reached Soren, while emails from Soren to me were intercepted by crooked Jeff, and passed on to me through his fake email address.
The Crucial Step - Changing the Bank Account Details
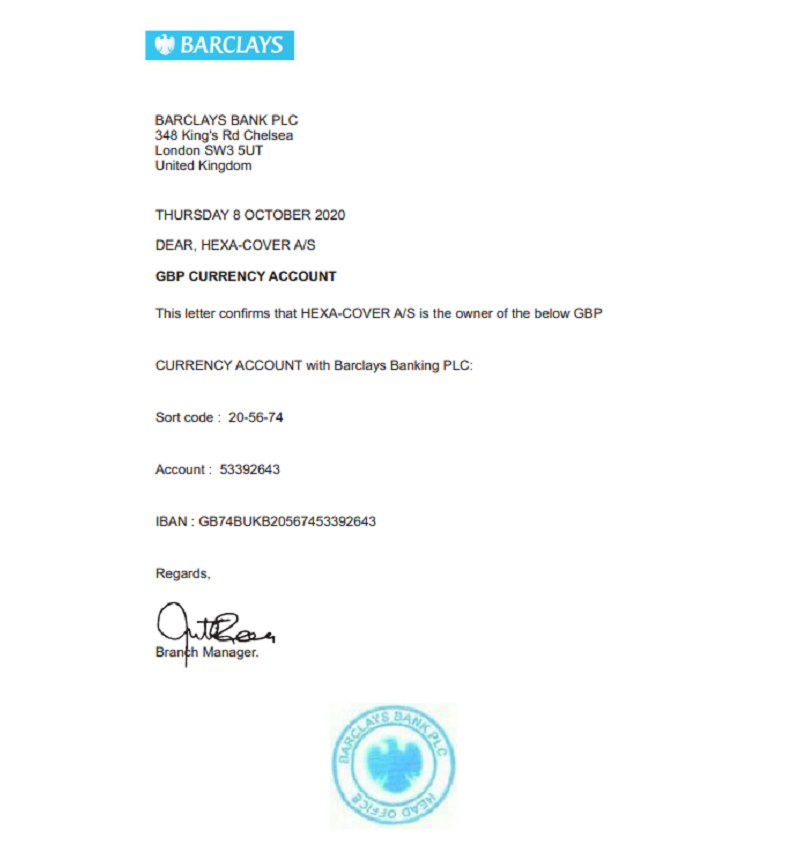
At this point the fraud reached its pivotal point. Crooked Jeff wrote to me about a problem in transferring the funds from Israel to the Danish bank account, and requested that payment be instead sent to the company’s account in Barclays Bank in London.
This seemed odd to me. But instead of phoning Soren in Denmark, or at least sending a text message - I emailed Soren.
I asked if the email I received wasn’t a fake. And crooked Jeff, writing as Soren, assured me that wasn’t the case. In retrospect, with hindsight, it’s easy to see this was a big mistake.
But this wasn’t the end. I asked Soren (or really, crooked Jeff) to send me official confirmation from Barclays Bank in London that the aforementioned account did indeed belong to Hexa-Cover. This was supplied shortly after.
This will prove to be a key step, ensuring our happy ending.
See this confirmation below:
Delivery and Payment to London
After a few weeks, the first container arrived in Israel (you can see a short video of its unloading and deployment here).
A week later the second container arrived, and the client transferred the payment - to the London bank, not the Denmark account. On the Friday of the second week, Soren wrote to me that he didn't see the first payment in the company’s account.
A red flag started waving, and I sent him the email where he (I believed) asked that payment be sent to the London account.
Soren called me immediately. He said it was a fake. The first thing to do was stop the second payment, so that it wouldn't be sent to the fraudulent account.
Friday around noon, the client’s CFO called the Bank of Israel, which quickly acted to stop the payment (which was already on its way).
On his end, Soren called Barclays, introduced himself, and asked to receive the money in Hexa-Cover’s account. I doubt they believed him, but in any case the money was already gone.
We were able to find out the fake domain was bought in Florida by a man named Jeff. But this information was useless. We tried to get recompense through both the client’s insurance company, and Hexa-Cover’s. But despite both companies insuring against cyber fraud, they found ways to avoid payment.
The Happy Ending
After a few months, the Bank of Israel, through which the money was transferred, sent Barclays Bank in London all the relevant information, and asked for their position in the matter.
Within days, the latter said they’ll return the full amount stolen.
It’s unclear why, exactly, but I think it’s because Barclays realized they made a mistake (or perhaps even violated regulations) allowing the fraudulent account to be opened (with no confirmation it was actually done by the company in whose name it was) and were worried the Bank of Israel might act to correct it.
After all, can you open a bank account with no form of identification?
Is This the Only Cyber fraud You’ve Heard of?
Cyber fraud like this is common. Over the last few months I’ve heard of a company that ordered machinery from Bulgaria. After a few months they were told the machine was ready, and to transfer payment to so-and-so bank. They did so, and awaited delivery.
And then, after a few weeks, they were told by the (real) supplier the machine was ready, and to transfer payment…
By that point, it was too late to find the payment sent to the fraudulent account.
A similar thing happened to a large company, which transferred 600,000 dollars to a fraudulent account.
Let’s go back to the beginning of this article, to the phone call I got from Yossi the investigator. He found me after investigating fraud on behalf of an Israeli company which hired him. He told me he discovered approximately 20 cases of fraud, like my case, which happened all over the world in the last year. In a follow-up talk, he told me that Barclays Bank London was involved in the case he was investigating, too.
Summary and Recommendations
Cyber fraud happens. It seems insuring against it is an important step, as long as, of course, the insurance company will actually compensate you, and with a reasonable amount.
In any deal with a company that has an accounting department, we are required to send confirmation from the bank that the account is in our name.
It turns out such confirmation isn’t enough, at least not when dealing with companies overseas.
In addition to written communication with the supplier, or confirmation from their bank - the most important step with any request to change a bank account, or to register a new one - is to phone the supplier and confirm the details verbally.
This type of two-step confirmation is called MFA, or multi-factor authentication. In many situations, we are required to confirm our identity with a code sent over text message or email, in addition to login information.
So why isn’t this the procedure when it comes to payments and money transfers?









 My First Book: Manage! Best Value Practices for Effective Management
My First Book: Manage! Best Value Practices for Effective Management